Backup Computer Data System
Your company needs to setup a system for assure backup computer data.
Most companies fully back up files on LANs and engineering workstations as a standard in today's business environment. However, companies commonly overlook backing up data files on stand-alone PCs.
The chances of a hard drive crash or a virus affecting your vital PC records occur far greater than a catastrophic event. Vital PC data files should be backed up and stored off site regularly. This improves recovery time and effort, and decreases the possibility of an extended business interruption or service reduction.
Vital PC records could include phone lists, financial records, project proposals, cost models, and many types of other important data. If no longer accessible, those records could interrupt daily business functions and increase the cost, time, and effort of full business recovery.
Employee Handbook Kit includes two Employee Handbook templates for Professional & Manufacturing. Includes over 60 policies and benefits templates.
Backup Computer Data Locations
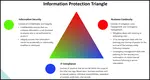
Three backups should be maintained for all vital PC data files. Two of these backups should be on-site. One of these should be stored in a secure and fire protected area for operational recovery. Lastly one should be stored off-site for disaster recovery. This is called the 3-2-1 system of backup.
Follow these recommendations for off-site storage facilities:
- The location should be far enough away so that it's not impacted by the disaster.
- Physical controls, such as security, authorized access, environmental (heat, humidity, water, frost, etc.), and fire protection should be in place.
- The facility should be accessible 24 hours a day, 365 days a year.
Once establishing the above controls, then document the backup procedures. Implement and teach these to the entire team of PC users. The documented backup procedures should include the following:
- Label all backup files should to identify their content.
-
Document methods for transporting the media.
-
Compile a list of those authorized to retrieve off-site backups.
- Create timetables for the creation and rotation of backup files.
Follow these steps to ensure that you are prepared. The time you take today could help avoid disaster tomorrow.
TrainingKeeper Software. Keep, organize and plan all your employees' training and activities. Software includes multi-user support with reports, certs, and calendars.
Backup System Questions
Creating and labeling daily, weekly, and/or monthly backups of your information, based on how difficult it might be to recover / re-create, can save hours of heartache.
The time to create a backup computer data can range from five minutes to many hours depending on the size of the system or set of information you desire to have backed up. Always identify the contents, the date of the backup, and the data classification.
The information backed up, the number of backups, and the frequency of backups depends on your answers to the following questions:
- What would happen to my business, my customer, and my colleagues if I lost this information and could not recover all or most of it?
- Has data been added / modified / removed since the last backup?
- Has there been a modification of the system, programs, or functions?
- Do we have a system that automatically copies / backup PC files and folders to the Server?
You should make backup copies of all original software soon after installation. Follow these tips and never have to say "It's Gone"!
|
Software, Videos, Manuals, On-Line Certifications | ||
|
450+ Editable Slides with support links | ||
|
Corrective Action Software | ||
|
Plan and Track Training | ||
|
AQL Inspection Software | ||
|
Learn and Train TRIZ |