Disaster Recovery Article
This disaster recovery article covers key aspects to consider when creating a contingency plan.
A disaster event causes an unplanned or extended interruption in service that has the potential to affect the operations or finances of the business or its customer. A disaster goes beyond the scope of daily operations or emergency response procedures.
A contingency plan responds to a disaster to ensure that support for critical business functions resume as quickly as possible. It minimizes lost dollars, transactions, and information.
This disaster recovery article wants you to ensure repair or replacement of the stricken facility as quickly as possible. When a disaster occurs, your company executes its contingency plan, which provides for recovering information processing services within agreed upon service-level requirements.
Employee Handbook Kit includes two Employee Handbook templates for Professional & Manufacturing. Includes over 60 policies and benefits templates.
Minimize Impact
Planning for the recovery and continuation of critical business functions after a service disruption is an increasingly important function.
Businesses use computers extensively and depend on them for daily business operations, thus, any service interruption is very undesirable.
To minimize the impact and risk of a service interruption, a company needs to
- identify business functions that are critical to the business,
- to define goals for contingency management
- implement quality prevention and recovery plans.
- A contingency plan plan should be documented for each company site.
The plan should describe the
- contingency plans
- required resources
- recovery procedures
- team responsibilities to recover services.

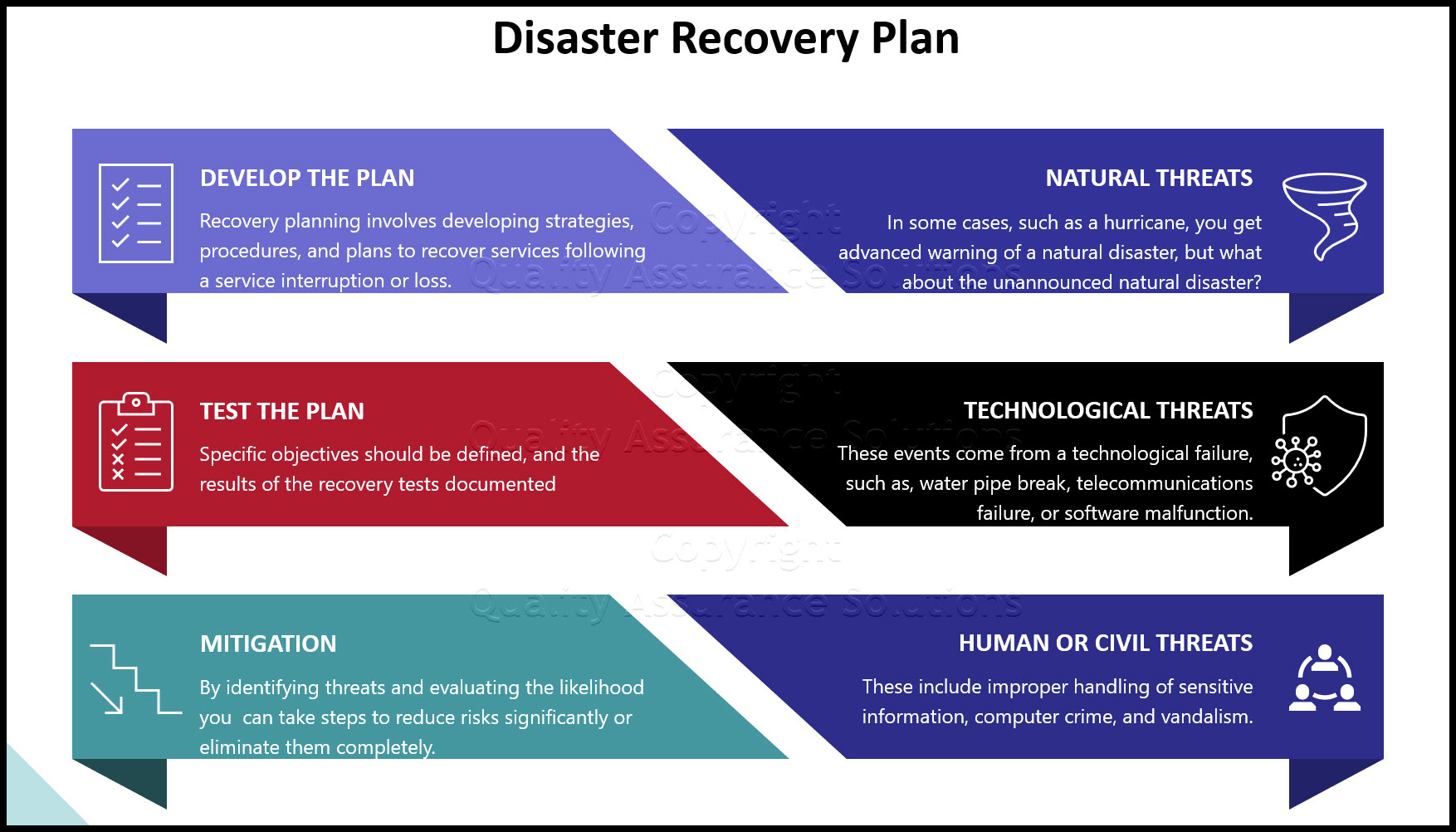
Recovery planning involves developing strategies, procedures, and plans to recover services following a service interruption or loss. It also involves translating service level requirements into technical solutions.
Recovery planning involves...
- the development of logically and physically related software
- hardware
- facilities
- network data,
- people
- processes
into a predefined set of solutions that facilitate service restoration over time.
Businesses should also ensure that the contingency / recovery plans integrate for their organizations, service providers, and customers, in order to result in effective recovery of information processing and services within customer defined requirements.
8D Manager Software with 8D, 9D, 5Y and 4M report generator. Your corrective action software for managing, measuring, and reporting issues.
Test the Plan
To improve the effectiveness and integration of recovery plans, businesses should test their recovery capabilities periodically. Specific objectives should be defined and the results of the recovery tests documented. Businesses should then review test results, suggest needed improvements, and submit business proposals which enhance the recovery process.
No solution is foolproof. As a prudent planner, you need to make allowances for the unexpected. Because business continuity is essential in virtually every e-business environment, you need to identify critical business processes and assets, and know what should trigger recovery procedures. It's also very important to identify which recovery roles and responsibilities belong to IT, and which are best assigned to other parts of the organization.
Mitigation - Reducing Risk
Identifying and reducing risks should concern us all. It is impossible to stop most natural disasters and many man-made disasters from occurring, but by identifying and documenting potential threats, evaluating the likelihood of them being realized, and determining our vulnerability to them, we can take steps to reduce risks significantly or eliminate them completely.
Common type disasters such as natural, technological, and human or civil threats are among the most common types that can cause serious service interruptions.
TrainingKeeper Software. Keep, organize and plan all your employees' training and activities. Software includes multi-user support with reports, certs, and calendars.
Natural Threats
In some cases such as a hurricane, meteorologists will give advanced warning that the threat of a natural disaster, but what about the unannounced natural disaster? What is the likelihood of each type of natural disaster happening in your area? Where do the vulnerabilities lie?
For example, for this disaster recovery article, In San Diego, California, a winter storm would be a low risk compared to the high risk of earthquakes. If an earthquake happens, what are the vulnerabilities of people, property, and service? Have you prepared for a possible evacuation, rescue of personnel, building damage, or communication loss?
Technological Threats
These events come from a technological failure, usually caused by human omission or error, such as, water pipe break, telecommunications failure, or software malfunction. Another example would be the risk of an explosion caused by leaving combustible material next to a welding area.
Can you take precautions to reduce the potential of these types of threats from occurring, or to reduce their impact if they do occur?
Disaster Recovery Article and Human or Civil Threats
Humans cause these types of events, either accidentally or deliberately. Examples for this disaster recovery article, include improper handling of sensitive information, computer crime, and vandalism. Has any thought been directed toward the probability of these types of threats being realized? What steps can be taken to reduce the risks?
The old saying "an ounce of prevention is worth a pound of cure" was never more true than in the identification, evaluation, and mitigation / elimination of risk. Would you take your family in a small boat with no life preservers, not have your car checked before taking a long trip, or not pay your car or homeowners insurance? Have you ever discussed with your family what you would do in case of a fire or tornado? We consider these responsibilities a normal part of daily life. The same should go for your job and business as well.
- QAS Home
- Risk Management
- Disaster Recovery Article
|
Software, Videos, Manuals, On-Line Certifications | ||
|
450+ Editable Slides with support links | ||
|
Corrective Action Software | ||
|
Plan and Track Training | ||
|
AQL Inspection Software | ||
|
Learn and Train TRIZ |